Modern software development depends on an intricate web of third-party libraries, frameworks, and transitive packages. While these dependencies accelerate innovation, they also introduce security, stability, and maintenance risks. Dependency update platforms have emerged as structured, automated solutions for managing this complexity at scale. They systematically monitor, test, and apply updates, reducing manual effort while strengthening security posture and operational resilience.
TLDR: Dependency update platforms automate the monitoring, testing, and application of software library updates. They reduce security vulnerabilities, minimize technical debt, and improve development efficiency. By integrating with version control systems and CI/CD pipelines, these platforms provide controlled and auditable dependency management. Organizations adopting these tools experience safer releases and faster response to emerging threats.
In the past, updating dependencies was largely reactive. Development teams would only upgrade libraries when a problem surfaced, often introducing rushed changes and unintended breakages. Today, with increasing regulatory scrutiny and cyber risk, a proactive approach is essential. Dependency update platforms provide this framework by continuously analyzing repositories, identifying outdated components, and suggesting or automatically creating update proposals.
The Growing Risk of Dependency Sprawl
Applications no longer consist solely of proprietary code. Studies consistently show that open-source components account for the majority of modern codebases. Each dependency can itself rely on dozens of nested packages, forming a complex dependency graph. This interconnected structure leads to:
- Security vulnerabilities introduced by outdated or compromised packages
- Version conflicts that destabilize builds and deployments
- Compliance risks due to incompatible or untracked licenses
- Operational fragility when maintainers discontinue support
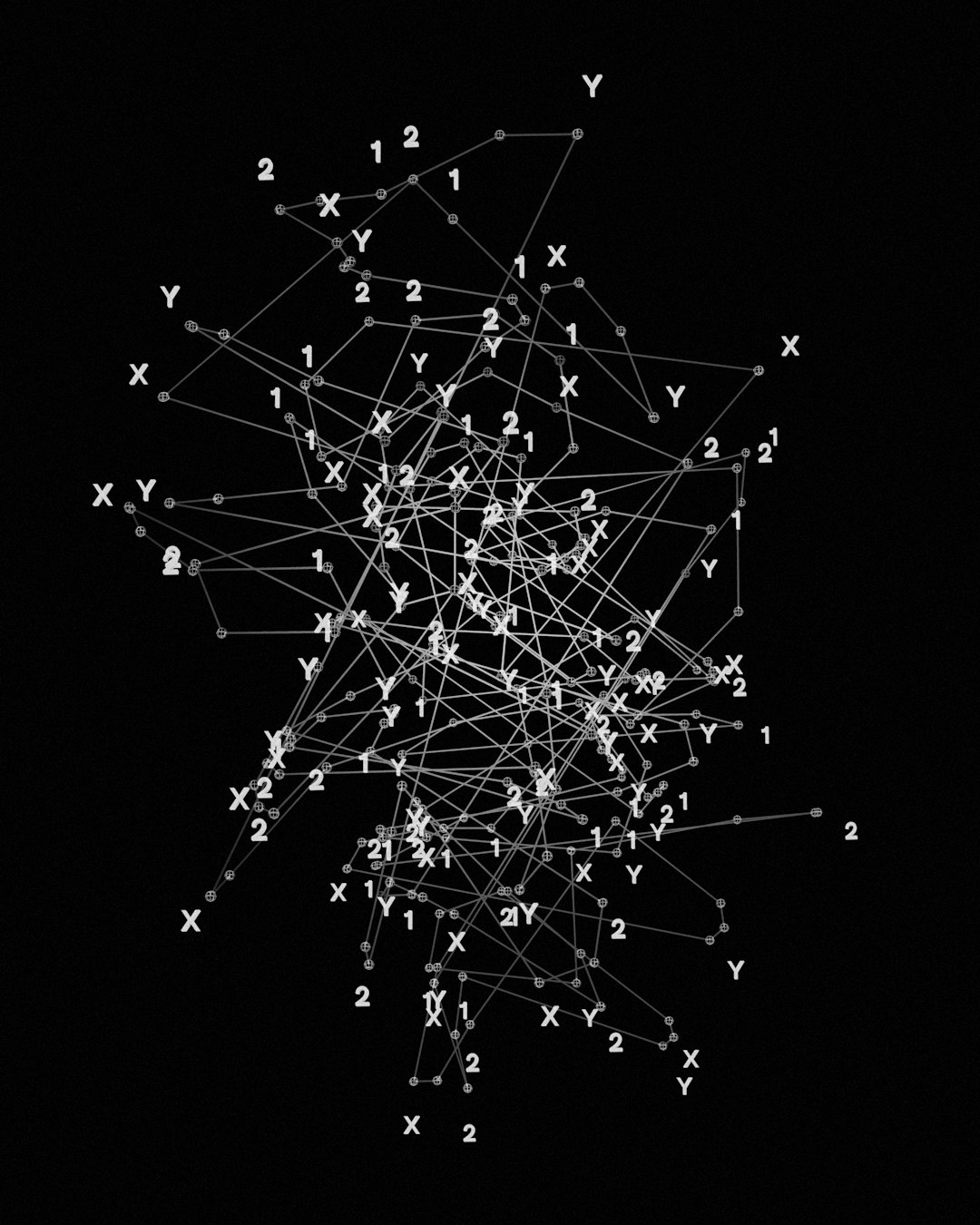
Without structured oversight, teams lose visibility into what their applications truly depend on. A single unpatched vulnerability in a deep transitive dependency can expose entire systems to attack. Dependency update platforms address this challenge by improving transparency and bringing automation to what would otherwise be an overwhelming manual task.
Core Capabilities of Dependency Update Platforms
While implementations vary, robust dependency update platforms typically provide a set of foundational capabilities designed to support enterprise-grade development workflows.
1. Automated Monitoring
The platform continuously scans code repositories and compares dependency versions against official registries. When updates become available—whether bug fixes, minor enhancements, or major releases—the system generates alerts or pull requests.
This monitoring often includes:
- Real-time tracking of newly published versions
- Identification of deprecated packages
- Mapping of dependency trees, including transitive components
2. Security Intelligence Integration
Leading platforms integrate with vulnerability databases and threat intelligence feeds. When a known security flaw is disclosed, the system correlates it with affected projects and recommends upgrades. This significantly shortens the exposure window between vulnerability disclosure and remediation.
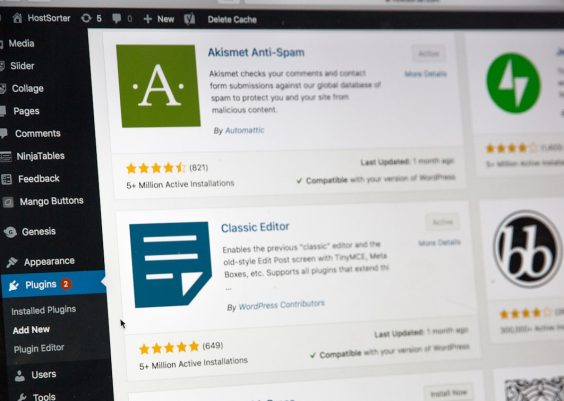
3. Automated Pull Requests
A defining feature of dependency update platforms is their ability to generate structured pull or merge requests automatically. These requests often include:
- Release notes summarizing changes
- Risk classification (major, minor, patch)
- Links to relevant advisories
- Suggested configuration adjustments
By framing updates within familiar development workflows, these platforms minimize adoption friction.
4. CI/CD Integration and Testing
Updates alone are insufficient; they must be verified. Integration with continuous integration pipelines ensures that every proposed dependency change is tested automatically. Build failures or regression issues are surfaced before manual review, preserving code stability.

5. Policy and Governance Controls
Enterprise adoption requires governance capabilities. Mature platforms allow administrators to define update policies, such as:
- Auto-merging minor updates after successful tests
- Restricting major version upgrades for manual approval
- Applying schedules to avoid disruptive changes during peak cycles
- Enforcing license compliance criteria
These controls maintain operational discipline while preserving automation benefits.
Strategic Benefits for Organizations
Implementing a dependency update platform yields both tactical and strategic advantages.
Improved Security Posture
Attackers frequently target known vulnerabilities with publicly available exploits. Organizations that delay updates expose themselves unnecessarily. Automated update mechanisms reduce mean time to remediation and strengthen defensive posture.
Reduced Technical Debt
Outdated dependencies accumulate over time, making future upgrades more complex and risky. Continuous incremental updates are significantly easier to manage than multi-year version jumps. Platforms encourage a culture of small, manageable change.
Operational Efficiency
Manual tracking of dependency versions across multiple repositories consumes valuable engineering resources. Automation frees teams to focus on value-producing development rather than maintenance overhead.
Enhanced Auditability and Compliance
Many industries require evidence of vulnerability management processes. Dependency update platforms create detailed logs of updates, approvals, and remediation timelines, supporting audit and regulatory reporting requirements.
Implementation Considerations
Successfully deploying a dependency update platform requires thoughtful planning.
First, organizations should assess repository diversity. Multi-language environments may require broader ecosystem support. A tool that works well for JavaScript may not cover container images or infrastructure-as-code dependencies.
Second, teams must address update fatigue. An overly aggressive configuration can overwhelm developers with excessive pull requests. Proper grouping strategies and prioritization help maintain balance.
Third, it is essential to embed updates within testing and release workflows. Automation without testing increases risk. When paired with robust CI pipelines, however, dependency updates become predictable and manageable events rather than emergency responses.

Best Practices for Sustainable Dependency Management
To maximize return on investment, organizations should follow disciplined operational practices:
- Adopt incremental update cycles rather than batching extensive upgrades.
- Establish clear ownership for dependency management within teams.
- Maintain comprehensive test coverage to reduce fear of automated updates.
- Review major version changes carefully for breaking modifications.
- Combine automation with human oversight for high-impact components.
Additionally, communication within engineering teams is critical. Transparent reporting on dependency health metrics fosters shared accountability and continuous improvement.
Challenges and Limitations
Dependency update platforms are not a complete solution in isolation. Certain challenges remain:
- Breaking Changes: Major updates may require code refactoring beyond automated fixes.
- False Positives: Not every reported vulnerability is exploitable in a given context.
- Third-Party Reliability: If maintainers abandon a package, alternatives may need evaluation.
- Performance Considerations: New versions can introduce unexpected performance regressions.
A mature approach combines automated monitoring with architectural awareness and security expertise. Organizations should treat dependency management as a living process rather than a one-time configuration.
The Future of Dependency Update Platforms
As software supply chain security gains prominence, dependency update platforms are evolving. Emerging capabilities include:
- Provenance verification through signed packages and attestations
- AI-assisted risk scoring to prioritize high-impact updates
- Deeper integration with container and infrastructure dependencies
- Automated rollback mechanisms in case of deployment instability
The focus is shifting from simple version tracking to comprehensive supply chain integrity. Organizations that anticipate this shift will be better positioned to manage regulatory expectations and defend against sophisticated threats.
Conclusion
Effective dependency management is no longer optional; it is foundational to secure and maintainable software systems. Dependency update platforms bring structure, automation, and governance to a historically neglected area of engineering practice. By integrating monitoring, security intelligence, automated testing, and policy controls, these platforms reduce risk while preserving development velocity.
For organizations seeking long-term resilience, the path forward is clear: adopt automated dependency update solutions, reinforce them with disciplined workflows, and treat dependency health as a continuous operational responsibility. In doing so, businesses transform dependency maintenance from a reactive burden into a strategic advantage.